secloud elimino
secloud elimino is our secure data erasure solution where you get tamper-proof certificates and can erase any device from anywhere at any time.
End-user device security
With our device lifecycle management tools you’ll
Be able to make qualified decision on how to optimize the lifecycle of your devices.
Lifecycle device management
Features overview
📊 Dashboards, Insights & Control
- Webapp user dashboard – Intuitive UI for managing assets, users, security alerts, and tasks.
- Custom charts and reporting – Visual dashboards and tailored exportable reports.
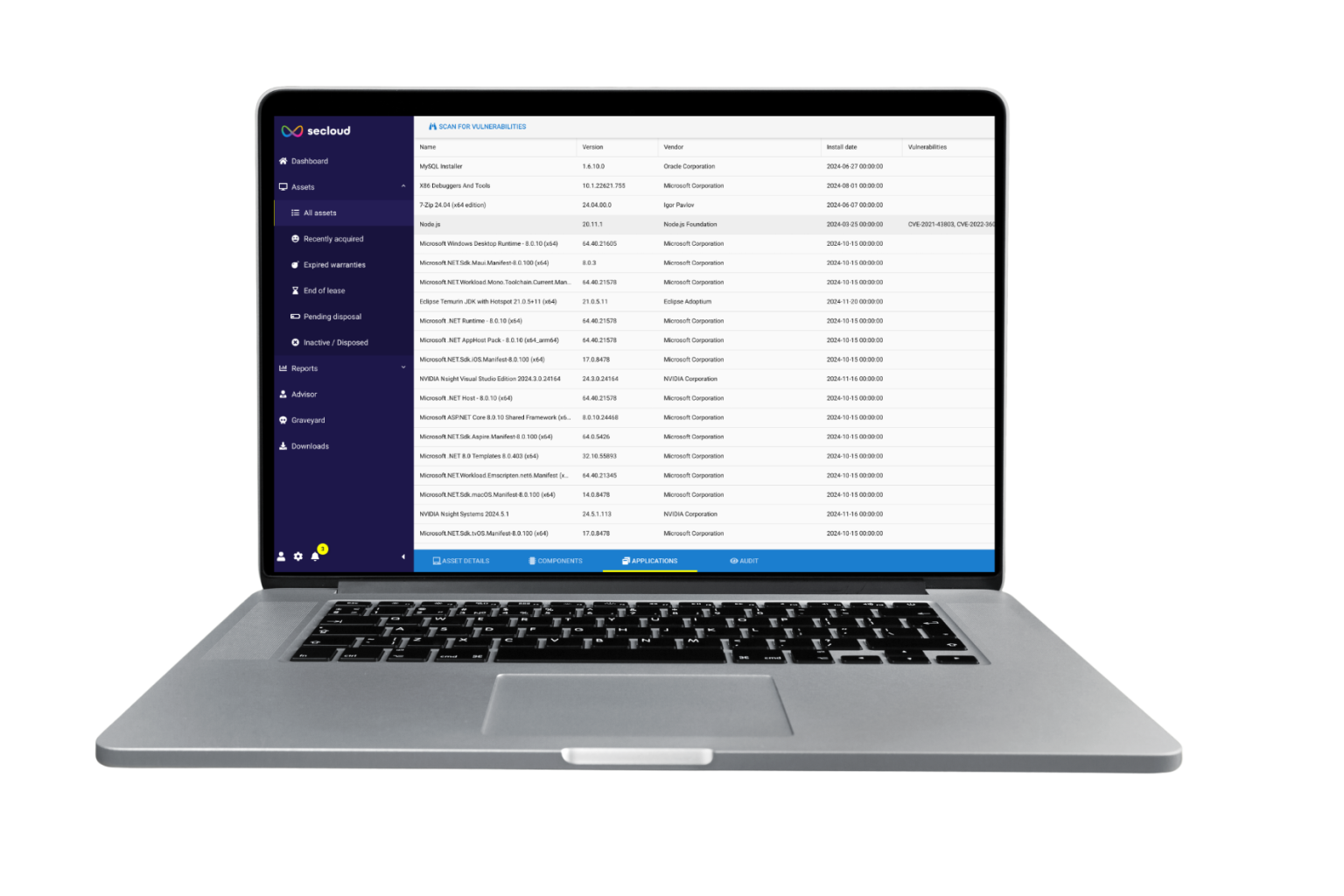
- Browse installed software – Full list of apps installed on any device for audits and licensing.
- Role-based access control – Ensure only authorized users can access certain features or data.
Device & Asset Management
- Asset management – Centralized tracking of all devices with full visibility across the organization.
- Filterable asset overview – Easily locate assets by status, location, or custom tags.
- Automatic enrolment – Seamless onboarding of new devices without manual steps.
- Company, office and group hierarchy – Reflects organizational structure for granular policy control.
- User allocation – Assigns devices to users or roles for clear ownership and auditability.
- Hardware component overview – Full inventory of hardware specs like RAM, CPU, storage, and more.
- Service and maintenance overview – Logs and tracks repairs, replacements, and service timelines.
- Warranty end report – Notifies you when devices near warranty expiration for proactive planning.
- Custom asset tags – Add metadata and business-specific labels for sorting and reporting.
- Asset valuation – Estimate remaining value of devices for resale or accounting purposes.
- Graveyard overview – Historical log of decommissioned or retired devices and erasure status.
Cybersecurity & Compliance
- Cyber security – Continuously monitors devices for vulnerabilities and security posture.
- Verified erasure – Meets international standards (NIST 800-88, ISO 27001) with logged proof.
- CISA known exploited vulnerabilities – Automatically flags threats linked to CISA advisories.
- Vulnerability score – Real-time device risk ratings based on software and configuration.
- Insecure network alerts – Warns when devices connect to suspicious or unsecured networks.
- Remote encryption – Lock down remote devices with full-disk encryption for data protection.
- Remote kill-pill – Instantly wipe or disable compromised devices to prevent data leakage.
- Geolocation – Shows real-time device location globally for inventory or incident response.
- Geofencing – Set physical boundaries and trigger alerts or actions if breached.
- OS user logging – Tracks active users on each OS for accountability and forensic purposes.
- Audit queries and user activities – Run reports to see who accessed what and when.
- Security and device advisory – Offers recommended actions to improve device posture.
Data Erasure – Certified & Flexible
- Access to remote certified data erasure (pay per erasure) – On-demand erasure billed per device.
- Secure remote erasure – Perform certified wipes from anywhere without retrieving the device.
- Secure on-site erasure – Perform compliant erasure locally, tracked from the platform.
- Tamper-proof erasure certificates – Receive digitally signed proof of secure erasure.
- Secure remote erasure – keeping OS intact – Only user data is wiped; OS remains for redeployment.
- NATO Certified data erasure – Military-grade wipe processes meeting NATO requirements.
- Extensive support of different OS and disks – Compatible with Windows, macOS, Linux, and all disk formats.